SaaS Architecture Decisions You Can’t Easily Walk Back — What Every Tech Leader Must Know
SaaS Architecture Decisions You Can’t Easily Walk Back — What Every Tech Leader Must Know
Table of Contents
Tenancy Model: The Enterprise Sales Wildcard
Database Schema Design: Where Product Flexibility Lives or Dies
Integration Patterns: Optionality vs. Lock-In
Frontend Architecture: The Hidden Bottleneck of UX Velocity
Authorization Models: The Enterprise Gate You Didn’t See Coming
How These Decisions Compound Into Strategic Risk
Final Thought
FAQs
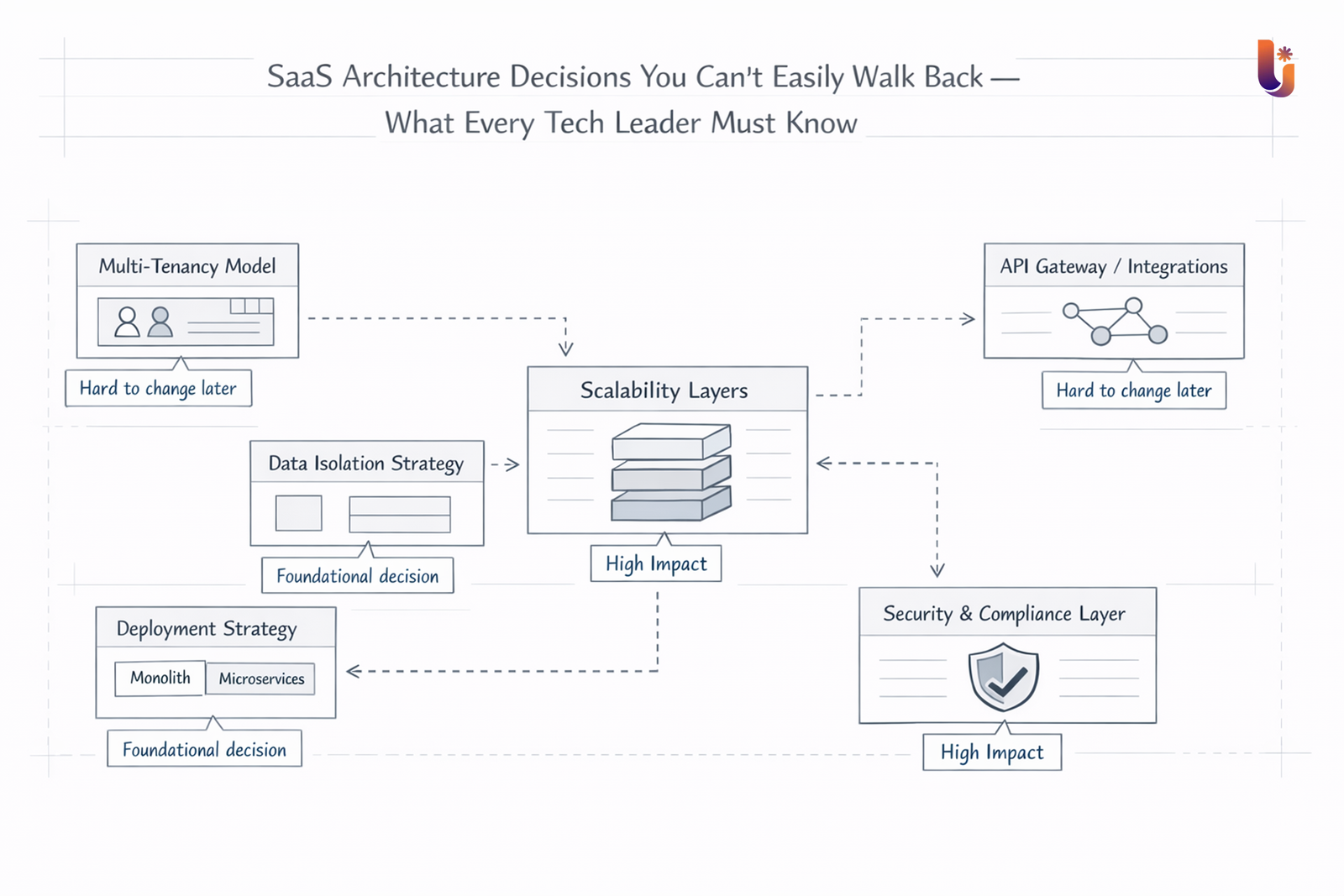
Most SaaS products don’t fail because of bad ideas. They stall because of invisible structural choices made months — sometimes years — before the cracks appear.
At Lumestea, we work closely with growth-stage SaaS teams navigating exactly this challenge. What we see again and again is this: the decisions that seem reversible during a fast-paced early sprint quietly become the constraints that slow every sprint that follows.
Infrastructure and cloud choices can introduce technical debt silently. SaaS architecture does the same — only it compounds faster because your customers are living inside the system while it’s evolving beneath them.
This guide breaks down the six most consequential SaaS architecture decisions, why each one is hard to undo, and what forward-thinking teams do differently.
1. Tenancy Model: The Enterprise Sales Wildcard
Your tenancy model — how customer data is isolated, provisioned, and operated — is one of the earliest structural commitments you make. And it reaches far beyond infrastructure.
Single-tenant deployments simplify compliance early on and can reassure security-conscious buyers. Multi-tenant architectures lower operational overhead and improve resource efficiency. Hybrid models offer the best of both worlds — but demand significantly more governance discipline.
The real pain emerges when your target customer profile evolves.
Teams that launch with single-tenant infrastructure and then pivot toward volume enterprise contracts face a painful rearchitecture: data models need rebuilding, access controls need redesigning, and infrastructure consolidation introduces new operational risk.
Going the other direction — starting multi-tenant and then needing true data isolation — drives infrastructure costs up and complicates compliance.
What forward-thinking teams do: Treat tenancy as a business decision built into code. Align tenancy architecture with your two-year customer profile, not your Day 1 launch checklist.
Impact on: Enterprise sales velocity · Compliance posture · Infrastructure cost structure · Operational scalability
2. Database Schema Design: Where Product Flexibility Lives or Dies
Schema decisions made at speed often feel inconsequential in the early days. In reality, they’re among the most expensive structural choices a SaaS company makes.
When teams optimize for launch timelines — tightly coupling tables, hard-coding relationships, embedding business rules directly into data structures — they’re trading future product flexibility for present-day speed.
As a SaaS product matures, new product directions demand more from the underlying data model:
- Configurable, workflow-driven product experiences
- Usage-based or hybrid pricing models
- Advanced reporting and customer analytics
- Granular, role-level permission systems
When the schema doesn’t support these needs natively, each new capability requires deeper structural changes. Production data migrations add risk. Release cycles stretch longer. Engineering effort shifts from building new value to maintaining structural workarounds.
What forward-thinking teams do: Design schemas that reflect where the product is heading — not just what it does today. Data architecture is product strategy expressed in tables and relationships.
3. Integration Patterns: Optionality vs. Lock-In
Nearly every modern SaaS product is built on third-party services — payment processors, identity providers, messaging platforms, analytics engines, AI APIs. The question isn’t whether to use them. It’s how tightly you let them attach to your system.
When vendor-specific logic spreads directly through your codebase — hardwired into controllers, service layers, and business logic — replacing any one of those vendors becomes a product-level effort, not an integration swap.
Pricing changes. Performance degrades. A vendor exits the market or shifts focus. When that moment arrives, teams without abstraction boundaries face weeks or months of refactoring work.
The more durable architecture isolates all vendor dependencies behind internal service interfaces or abstraction layers. This approach requires more discipline upfront — but it preserves optionality at exactly the moments when you need it most.
What forward-thinking teams evaluate:
- Can any vendor be replaced without modifying core product workflows?
- Does external logic sit behind internal boundaries your team owns?
- Are there direct third-party couplings in the critical path of your product?
The bottom line: Without vendor abstraction, external providers quietly begin shaping your roadmap decisions.
4. Frontend Architecture: The Hidden Bottleneck of UX Velocity
SaaS architecture conversations often fixate on the backend. But frontend structure is just as consequential — particularly for subscription businesses where onboarding quality and UX refinement directly influence retention.
When presentation logic, application state, and business rules are tightly interleaved, modifying any one element creates downstream risk across the others. Teams become hesitant to ship UX changes because the cost of regression is unpredictable.
Over time, this translates into:
- Simple UX improvements requiring deep engineering involvement
- Slower release cadences as testing scope expands
- Teams avoiding experimentation due to the overhead of change
The compounding effect is significant. What should be incremental product refinements become engineering projects.
Modular frontend systems change this dynamic. Clear separation of concerns, shared component libraries, and consistent design systems allow teams to refine onboarding flows, test new dashboard layouts, and iterate on conversion pathways — without disturbing the core product.
For subscription businesses, where every percentage point of retention has measurable revenue impact, frontend architecture and user experience design must evolve together.
5. Authorization Models: The Enterprise Gate You Didn’t See Coming
Early SaaS products almost always start with simple role-based access: admin, member, viewer. It’s fast to implement and sufficient for early customers.
Enterprise accounts, however, operate differently. Their procurement and security teams expect:
- Feature-level and resource-level permission controls
- Custom role creation and management
- Cross-team or cross-department visibility rules
- Comprehensive audit logs for compliance and security review
Because authorization logic touches nearly every layer of an application — APIs, UI states, data queries, background jobs — retrofitting fine-grained controls into a rigid permission model is one of the most expensive structural changes a SaaS team can undertake.
Security risk increases during the transition. Engineering timelines expand. And enterprise deals that require these controls stall while the work is completed.
What forward-thinking teams do: Build extensible permission frameworks from the outset — even if advanced controls aren’t needed immediately. The structural investment protects enterprise sales readiness without requiring full implementation upfront.
6. How These Decisions Compound Into Strategic Risk
SaaS architecture rarely breaks in obvious, dramatic ways. The degradation is gradual:
- Release cycles become visibly slower
- Infrastructure costs scale faster than revenue
- Enterprise procurement stalls due to compliance or permission gaps
- Engineering roadmaps fill with rework rather than new capability
Each of these signals points to structural misalignment between the architecture and the product’s current demands.
Tech leaders who evaluate architecture against projected customer profiles and expected scale — rather than current state alone — have significantly more control over how these costs accrue.
Architecture defines how the organization operates as complexity grows. It determines whether scaling the product strengthens the system or begins to expose its limits.
Final Thought
In SaaS, architecture is the ground your product grows on.
Tenancy model, data schema design, integration boundaries, frontend structure, and authorization frameworks each shape how resilient — or rigid — your system becomes as the business scales.
Speed gets you to launch. Structural durability determines whether you can grow without constant architectural repair.
At Lumestea, we help SaaS teams make architecture decisions that hold under real-world growth pressure — not just under ideal conditions. If you’re evaluating your current foundation or planning a build from scratch, we’d welcome the conversation.
Frequently Asked Questions (FAQ)
Q1: What is SaaS architecture and why does it matter for scaling?
A: SaaS architecture is the structural design of how your software-as-a-service platform is built — covering tenancy models, data schema, integrations, frontend structure, and authorization. It matters for scaling because poor architectural choices create compounding technical debt: slower releases, rising infrastructure costs, and limited enterprise readiness.
Q2: What is the most common architecture mistake early-stage SaaS teams make?
A: Over-optimizing for launch speed at the cost of structural flexibility. Tight database coupling, monolithic permission models, and vendor-specific integrations embedded directly in core code all feel fast to implement early — and expensive to reverse as the product matures.
Q3: When should a SaaS company think about multi-tenancy vs. single-tenancy?
A: Ideally before your first major enterprise contract — not during one. The decision should reflect your two-to-three year customer profile and compliance requirements. Switching tenancy models after customers are on the platform is one of the most disruptive architectural changes a SaaS team can face.
Q4: How does frontend architecture affect SaaS growth?
A: Directly. In subscription businesses, UX quality drives activation and retention. A tightly coupled frontend slows teams down — small UX changes require deep engineering involvement, which means product experiments happen less often. Modular frontend systems let teams iterate faster without regression risk.
Q5: What is vendor lock-in in SaaS architecture and how do you avoid it?
A: Vendor lock-in occurs when third-party service logic is embedded throughout your codebase without abstraction. Replacing any one vendor then requires significant refactoring. The mitigation is isolating vendor dependencies behind internal service interfaces — so swapping providers doesn’t touch core product logic.
Q6: How do SaaS authorization models affect enterprise sales?
A: Enterprise buyers consistently require fine-grained permissions, audit logging, and custom role structures. If your authorization model doesn’t support these natively, deals either stall while engineering builds the capability or are lost entirely. Building extensible permission frameworks early preserves enterprise readiness without requiring full implementation upfront.
Q7: How does Lumestea approach SaaS architecture consulting?
A: We work with product and engineering leaders to evaluate existing architecture against real growth trajectories — identifying structural risks before they become revenue blockers. Whether you’re building from scratch or navigating a scaling inflection point, our goal is the same: foundations that hold under pressure.
Build a foundation that scales with you.
Lumestea works with SaaS teams to make architecture decisions that hold under real-world growth pressure — not just ideal conditions.